If you live and breathe Gmail and other Google services, your Google account is probably your most valuable online asset. With Google’s commendable security and privacy settings, you can rest assured that your remote work and all your important data are protected from cyber risks and other digital threats.
Google and its partners are working hard towards helping awareness on all security related matters. Take a look at the following key security settings that will help you dramatically increase the security of your Google account.
Google security – check and change your passwords regularly
Your passwords are your first line of defence against cybercrime and identity theft. Therefore, one easy and accessible way to protect your Google account is to create a strong unique password and have it changed regularly. This is one of the most critical steps you can take to protect your privacy.
Here are some of the best password practices to follow to secure your Google account:
- Establish a strong password for every account you use, combining letters, uppercase and lowercase ones, symbols and numbers
- Use Google Password Manager to store your passwords
- Take a password checkup test within Password Manager to verify your existent passwords; you will see results like vulnerabilities, compromised passwords, used passwords or weak passwords so you can adjust each and one of them accordingly
- Change your passwords and passwords FAQs when suggested
And here are the steps to follow to change your Google account password:
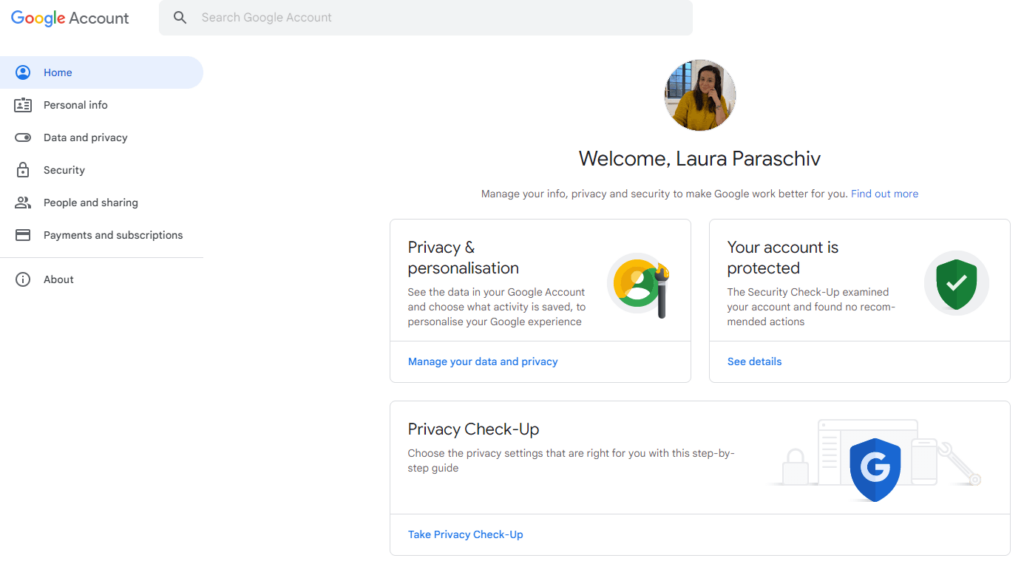
- Access ”Manage your Google account” from the upper right corner of any Google Workspace application like Gmail, Google Drive or Google Chat
- Navigate to the ”Security” tab in the left side menu
- Within ”Security”, you can scroll down until you see the password management section
- Click on the password label and re-enter your current password so Google can verify you
- Enter your new password, confirm it down below and select ”Change password”
- Remember, this new password will be not only your Gmail’s new password, but the password for all your Workspace applications
Why should you use 2-Step Verification for your Google accounts?
Securing just a password alone is useless without the extra security of a two-factor authentication, also called multiple-factor or multiple-step verification. With the 2-Step Verification, Google neutralises the risks associated with hacked accounts and actively involves the users in the process of remaining secure.
By adding this verification step, you can prevent cybercriminals from getting into your account, even if they can get past your password. One default 2-Step Verification that Google offers refers to receiving codes via text messages or directly on your phone or device. This way, you are verifying once more that it is you the user trying to access the account.
Here are the steps to set up the 2-Step Verification from the same ”Security” tab in your Google account manager:
- Click on the ”2-Step Verification” arrow to add an extra layer of security for the future.
- You can then select ”Get Started” button at the bottom of the page.
- At this next step, the Google security system will ask you to sign in once again. Click ”Next”.
- At the following page, you will be prompted to add your phone number that Google will only use for account security purposes.
- Next, choose whether you want to get Google’s secure codes via text message or a phone call or using a Google prompt on other signed in devices. Click ”Next”.
- At the following step, you will need to confirm the code you have received and click once more ”Next”.
- After this step, the secondary verification is now set up and you can start using this for all the apps onward.
After setting up the 2SV, you are still left with some other additional backup steps you can take. You can set up backup codes for signing in when away from the phone, buy a security key that can be built in your phone or set up devices that you can log on without a second step of verification.
Always log out of the device when you are not working
If you walk away from your computer and do not lock it, you are exposing all your sensitive data to security risks. Your smartphone or personal computer are highly personal pieces of equipment containing lots of important information.
Locking your screen and logging out of these devices when you are no longer working on them is the easiest way to prevent unauthorised access. All you have to do when resuming your activity is entering the password and picking up where you left off. Chromebooks are such smart devices running on Chrome OS. They only need your single Google account to get you resuming your whole activity on all Google accounts within.
Google Advanced Protection Program – why do you need it?
If you find yourself needing the strongest Google account security, you might need to enrol in the Advanced Protection Program. Usually, this technology is designed for people like journalists, activists or people with an elevated risk of targeted online attacks, but if your Workspace activity requires it, you can get it all for free.
How does Advanced Protection work?
- It prevents unauthorised access to your account, by requiring security keys for sign in.
- It provides extra protection from harmful files, by notifying or blocking stores, websites or downloads.
- It keeps your personal information secure by only allowing Google apps and verified third-party apps to access your data, and only with your permission.
How to turn on Advanced Protection?
You can only do it by using a built-in security key of an eligible device – Android or iOS phone. If you don’t have an eligible phone, you must purchase your security keys first and only after enrol in Advanced Protection.
Google recommends you getting 2 keys – a main key and the other as backup to store in a safe place. After purchasing the keys, turn on the 2-Step Verification and that Advanced Protection from your Google account.
FAQ
Use a strong, unique password or install a 2-Step Verification for extra protection.
Advanced Protection is recommended for anyone who is at an elevated risk of targeted online attacks.
At FOTC, we will guide you through each implementation phase and together we can determine which cloud solution will be the best answer to the needs of your business.
